
Julien Legras
@julien_legras
Pentest team leader @synacktiv
ID: 106076652
18-01-2010 12:28:41
640 Tweet
516 Followers
591 Following




For the second year in a row, we managed to get first place at the #HackTheBox Business #CTF 2025! 🥇 Congratulations to GMOサイバーセキュリティ byイエラエ株式会社【公式】 and Downscope and thanks to Hack The Box for the fun challenges! 🥳


To those who set the bar 🥂 Global Cyber Skills Benchmark 2025 is over, and the leaderboard has spoken. Huge congrats to the top corporate #cybersecurity teams who crushed it in this global competition: 🥇 Synacktiv 🥈 GMOセキュリティ24 |Webサイトリスク・パスワード漏洩診断 | セキュリティAI相談 🥉 downscope.org #HackTheBox





For the final talk of the Synacktiv track, Antoine Gql and Oposs give a retex on post-quantum cryptography #SSTIC2025



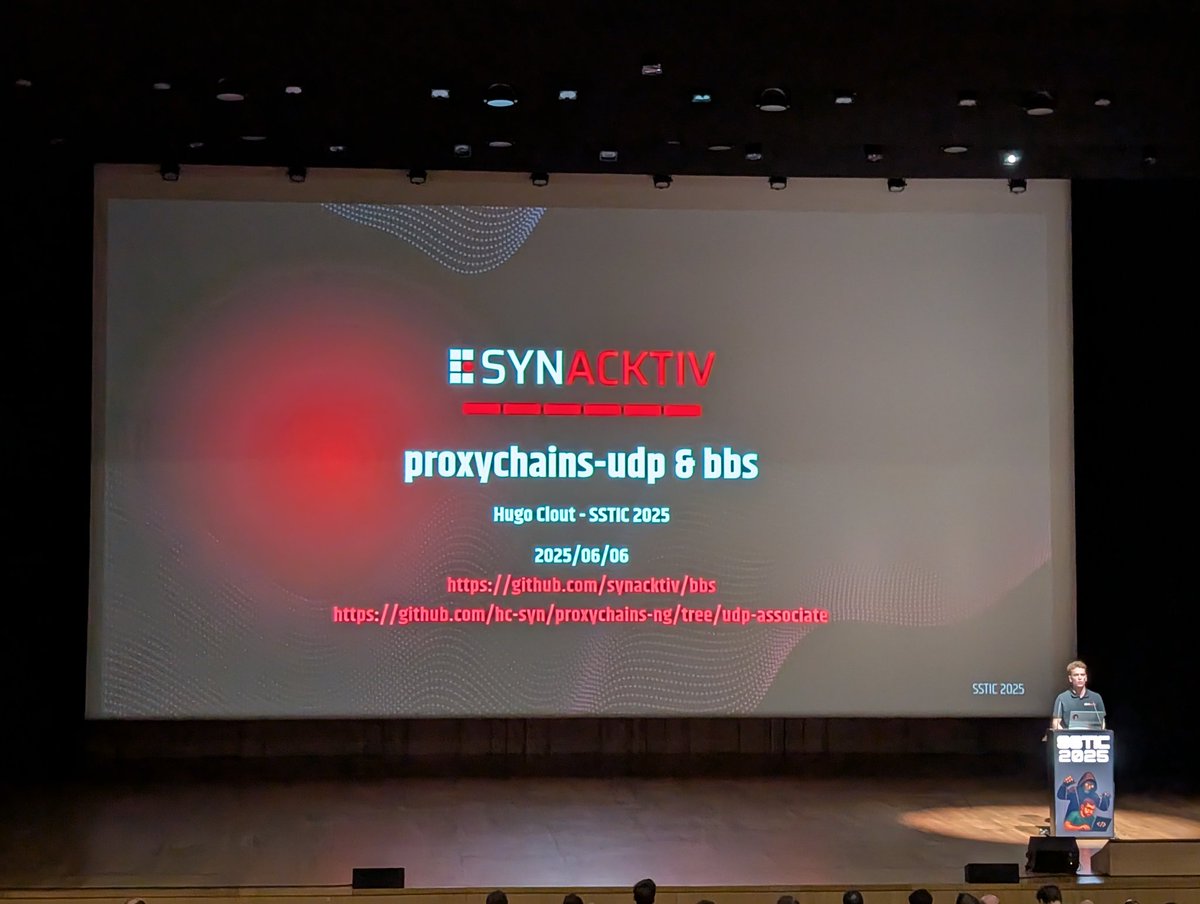
We still have a few talks for #SSTIC2025 last day! This morning, Hugo Clout presents 2 proxy tools used during pentests 🌐








Our experts took the stage at Pass the SALT Conference yesterday and this morning to present their latest offensive security research and tools! Keycloak, named pipes MITM and more! Slides and recordings coming soon 👀













