huli
@aszx87410
Taiwan / Front-end Engineer <=> Security Researcher. Interested in web. CTF player at @Water_Paddler
ID: 4731524647
https://blog.huli.tw/en/ 09-01-2016 03:51:10
2,2K Tweet
4,4K Followers
414 Following




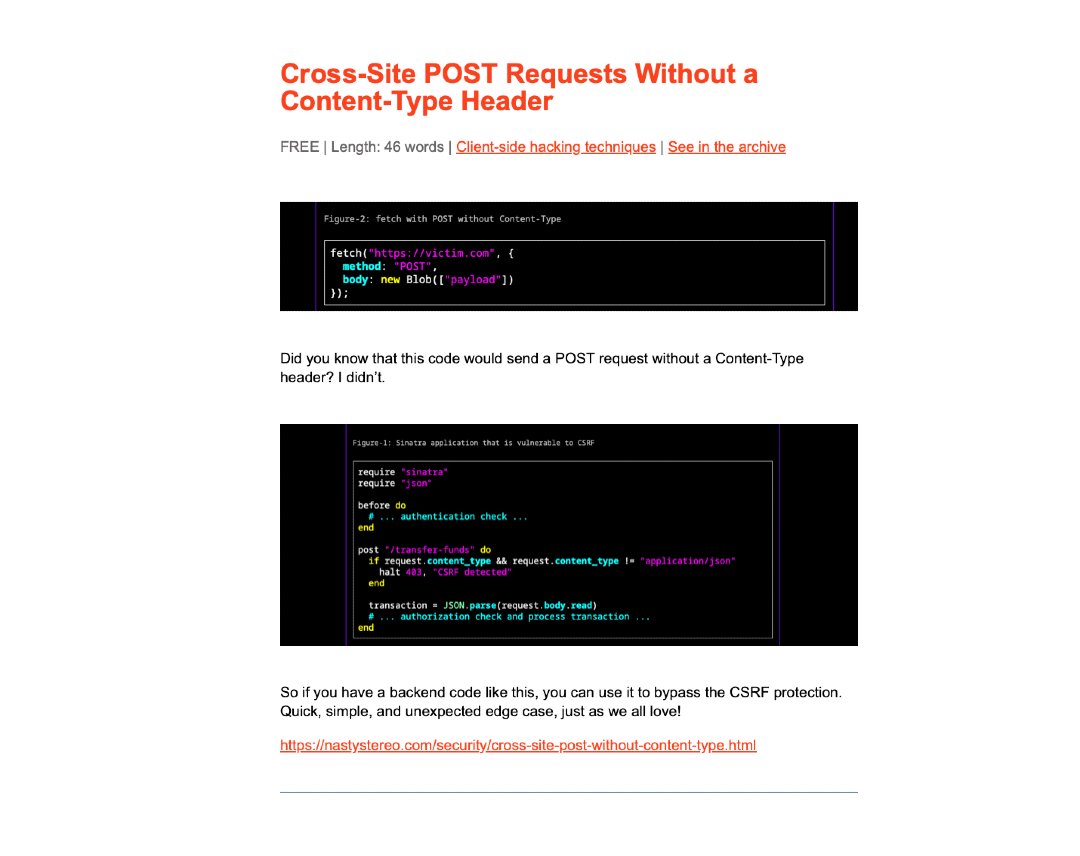
Cross-Site POST Requests Without a Content-Type Header by Luke Jahnke nastystereo.com/security/cross… #BBRENewsletter85










Double-Clickjacking, or "press buttons on other sites without preconditions". After seeing and experimenting with this technique for a while, I cooked up a variation that combines many small tricks and ends up being quite convincing. Here's a flexible PoC: jorianwoltjer.com/blog/p/hacking…

For this year Google CTF I created yet another Postviewer challenge called Postviewer v5². The challenge featured a seemingly impossible race-condition. Client-side race-conditions are an under-researched problem and could yield amazing real world bugs! gist.github.com/terjanq/e66c28…

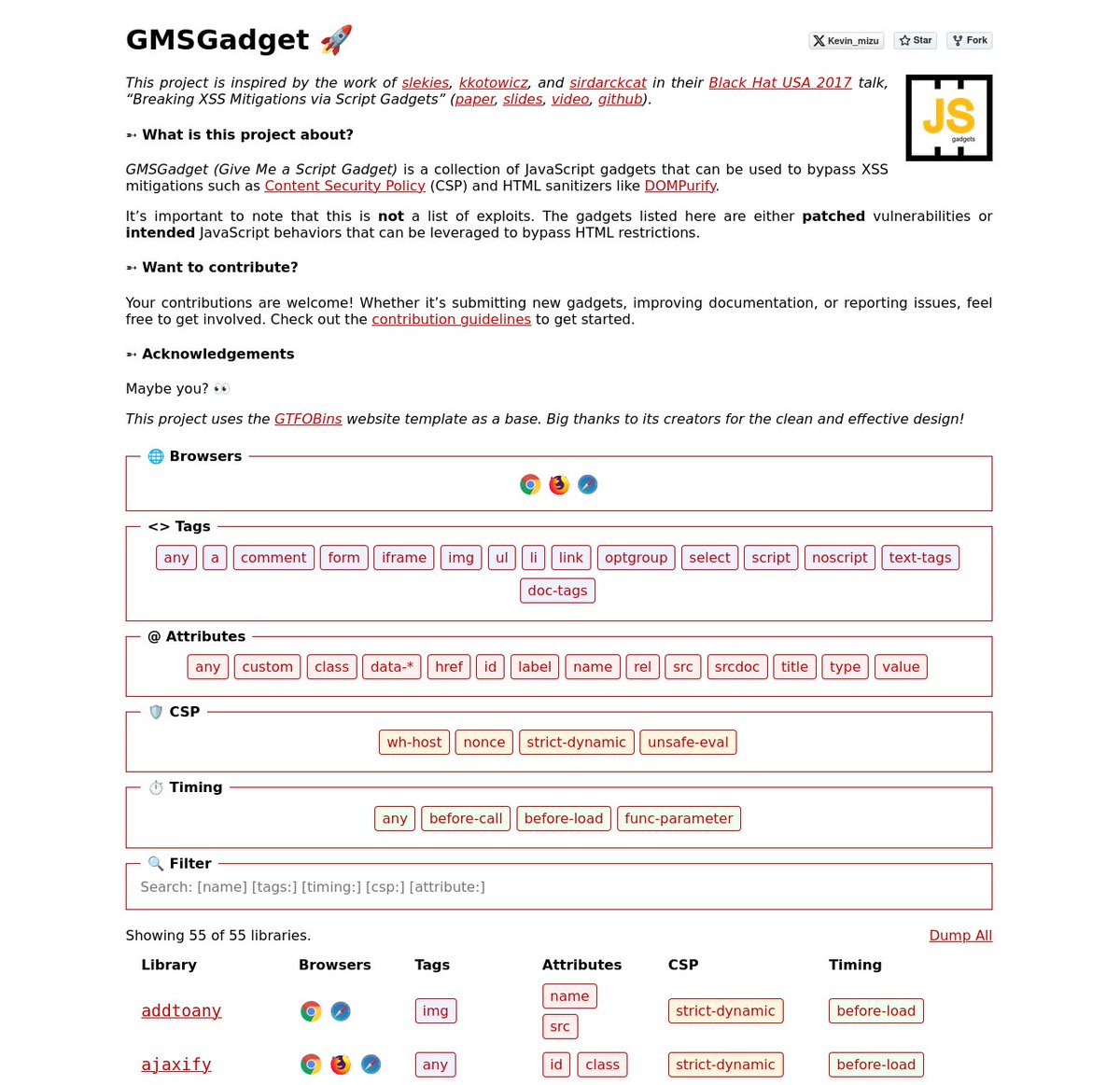
I'm happy to release a script gadgets wiki inspired by the work of Sebastian Lekies, koto, and Eduardo Vela in their Black Hat USA 2017 talk! 🔥 The goal is to provide quick access to gadgets that help bypass HTML sanitizers and CSPs 👇 gmsgadget.com 1/4


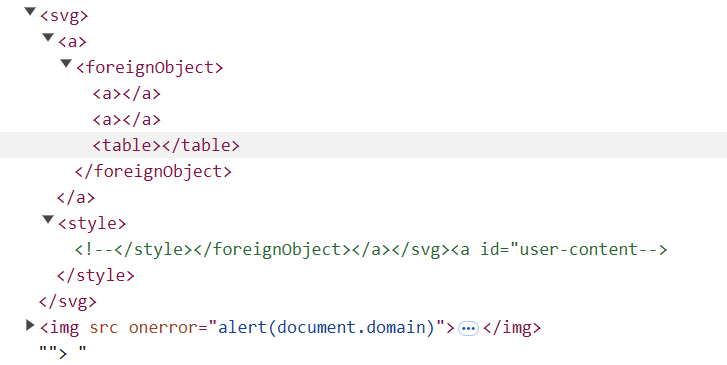
Last year I found a XSS bug in Google IDX here's a detail writeup about it. Hope you will enjoy it's kinda lengthy :p Shoutouts to Matan Berson for finding the original bug in Gitlab and Sreeram KL Sivanesh Ashok for the required chains to complete the exploit. sudistark.github.io/2025/07/02/idx…
"AI Agents for Offsec with Zero False Positives" by Brendan Dolan-Gavitt, a journey on how we managed to get 0 FPs with XBOW. You can find the slides for his BH talk here: cdn.prod.website-files.com/686c11d5bee015…