
Charlie Clark
@exploitph






Happy to finally share our slide deck/demo videos from our Texas Cyber Summit ®️ talk, “You DISliked DCSync? Wait For NetSync!” Thank you x3000 to Ashton Rodenhiser, for help with the fantastic slides, & my co-presenter/friend/mentor/research partner Charlie Clark 🤗 github.com/4ndr3w6/Presen…
Like the opsec of NightHawk but missing Aggressor-like scripting functionality? Check out DayBird, an extension I built for NightHawk to allow for automation of operator workflows and initial check-in actions via C# plugins. b:securityintelligence.com/x-force/extend… gh:github.com/xforcered/DayB…






Wow did not have “be in a book” for my 2024 🤯🤩 Thank you Denis Isakov! Thank you Charlie Clark for always including me in the journey of Kerberos with you 💜!
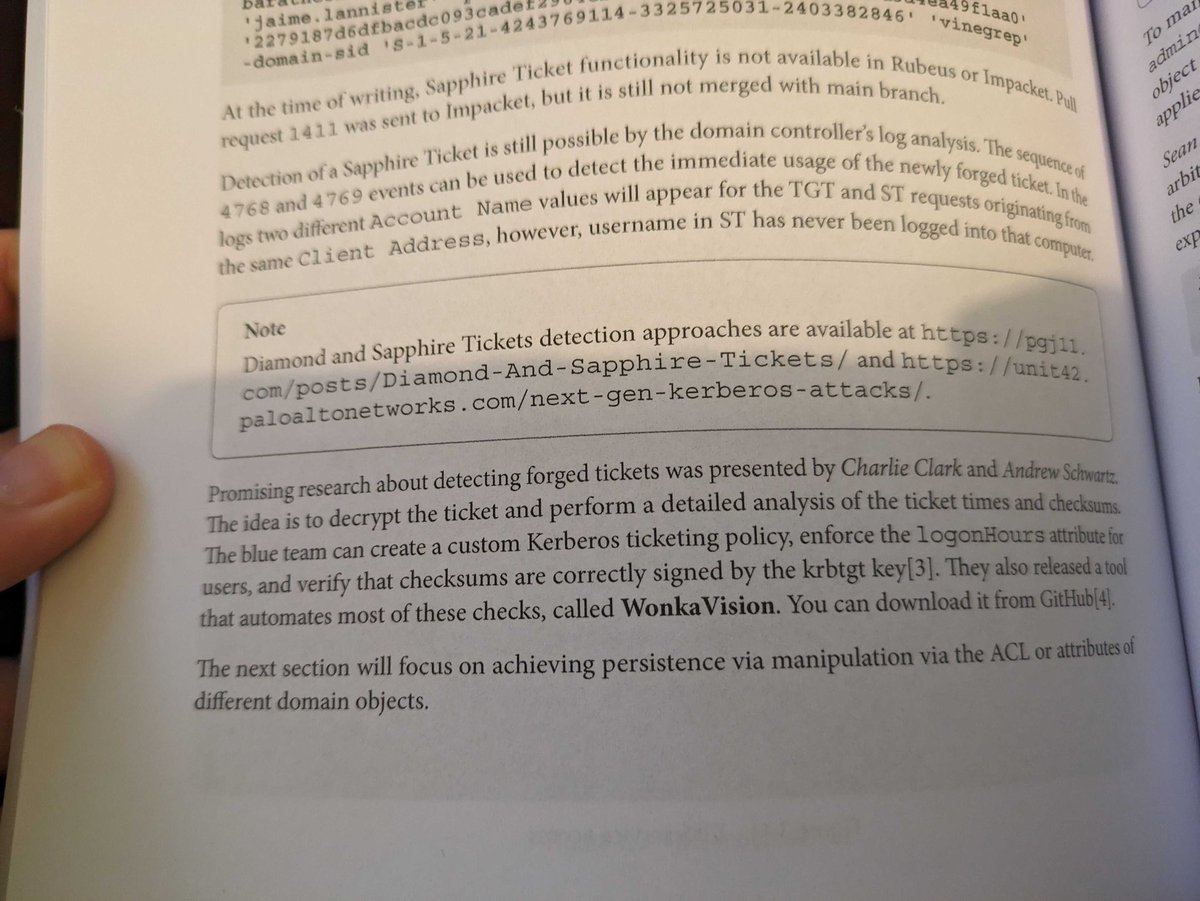







Happy to finally share a new blog with Charlie Clark on our work revisiting the Kerberos Diamond Ticket. ✅ /opsec for a more genuine flow ✅ /ldap to populate the PAC 🆕 Forge a diamond service ticket using an ST We finally gave it a proper cut 💎 huntress.com/blog/recutting…
