lazzslayer
@lazzslayer
Red Team | Co-Author of Redefining Hacking | VP for @bsidesnash | Advisory Board for @redteamvillage_ | OSCP, GCPN, CISM, GPEN | 🤠
ID: 1161404215857733632
https://infosec.exchange/@lazzslayer 13-08-2019 22:28:37
5,5K Tweet
4,4K Followers
580 Following


Would you help a struggling pregnant woman? At Out Of The Box Security Conference in Bangkok I’ll talk about how I’ve hidden networking gear in a fake pregnancy belly, posed as cleaning staff in C-Suite offices, and (ultimately) escalate physical breaches to domain admin.







The AD CS security landscape keeps evolving, and so does our tooling. 🛠️ Valdemar Carøe drops info on Certify 2.0, including a suite of new capabilities and refined usability improvements. ghst.ly/45IrBxI

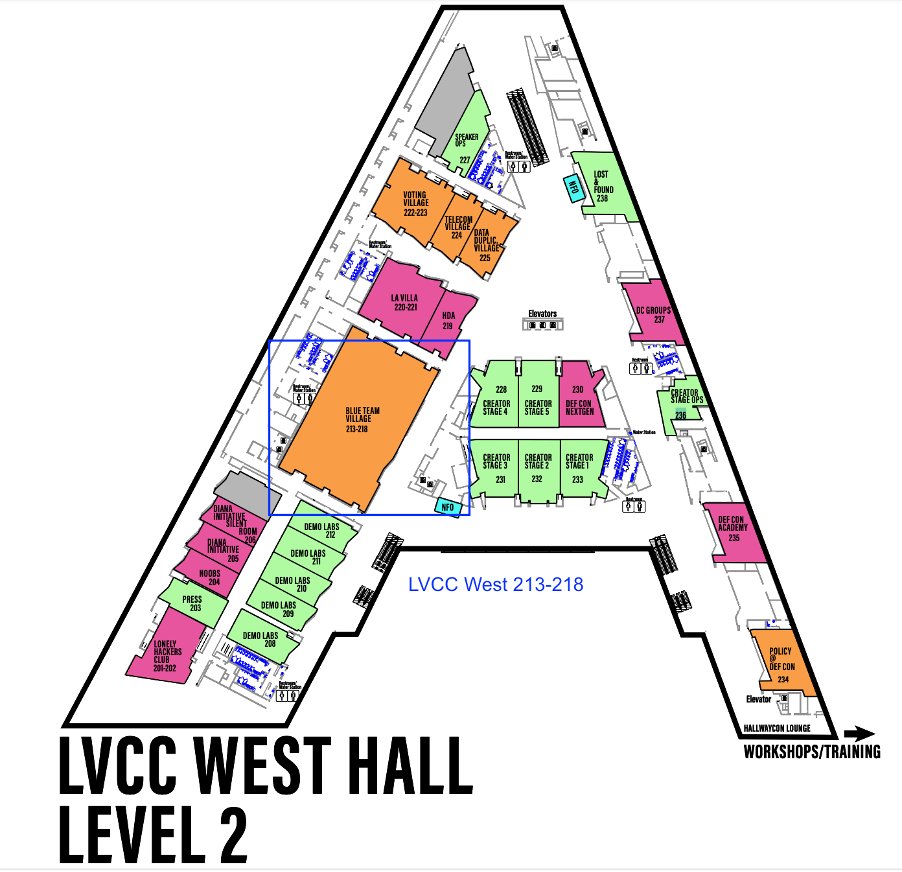
Had an amazing time at DEF CON. Massive thank you to RedTeamVillage and Bug Bounty Village for letting me be a part of their program this year! #defcon33